The holiday season brings joy…but it also brings unexpected cyber risks. Among the most dangerous are zero-day vulnerabilities, flaws exploited before patches are available. Combined with holiday distractions and increased online activity, these threats can turn festive cheer into costly breaches. Here’s how to strengthen your holiday cybersecurity strategy and stay ahead of zero-day attacks.
Why Zero-Day Vulnerabilities Surge During the Holidays
Cybercriminals know IT teams are stretched thin during December.
- Reduced Staff: Many IT professionals are on vacation, leaving fewer eyes on systems.
- Increased Online Transactions: Retailers and B2B platforms experience heavy traffic, making them prime targets.
- Delayed Patch Cycles: Organizations often postpone updates during peak business periods, creating exploitable gaps.
With remote work, vacation schedules, and heavy system loads, attackers exploit unpatched software and weak monitoring. Recent reports show that ransomware attacks spike by 30% during December, and zero-day exploits are often the entry point. These attacks can lead to data theft, operational shutdowns, and reputational damage.
Common Holiday Cyber Threats
The holidays aren’t just busy for businesses, they’re busy for hackers too. Companies are distracted. IT teams are short-staffed, everyone’s rushing to meet year-end goals, and security updates often get delayed. And hackers want to take advantage.
Common attacks look like:
- Phishing Emails: Holiday-themed scams trick employees into clicking malicious links.
- Third-Party Risks: Vendors and partners often introduce vulnerabilities during seasonal rushes.
- Unpatched Applications: Legacy systems and outdated software become easy targets for zero-day exploits.
5 Actionable Tips for Holiday Cybersecurity
Don’t let your business fall prey to holiday cybersecurity zero-day vulnerabilities this year. Use the tips below to prepare and protect.
- Prioritize Patch Management: Apply critical updates immediately to reduce exposure to zero-day flaws.
- Enable Threat Detection Tools: Use AI-driven monitoring for real-time anomaly detection.
- Educate Employees: Train staff to spot phishing attempts and suspicious links.
- Secure Remote Access: Implement MFA and VPNs for holiday remote workers.
- Prepare an Incident Response Plan: Ensure rapid containment and recovery if a breach occurs.
Bottom Line
Zero-day vulnerabilities don’t take holidays. By prioritizing holiday cybersecurity, your organization can enjoy the season without falling victim to unexpected cyber threats.
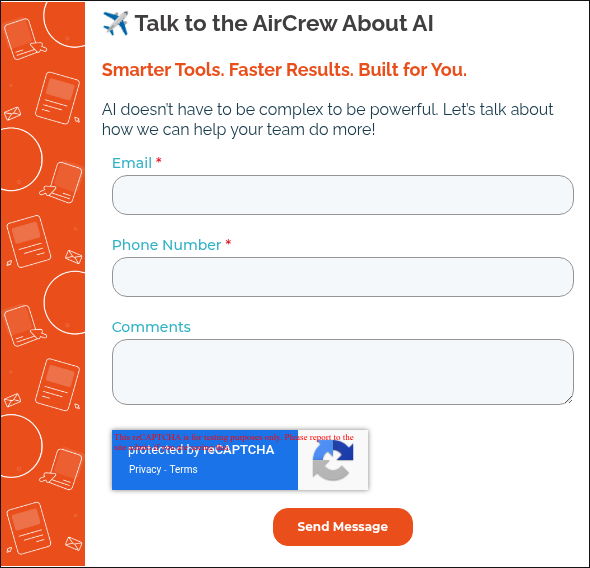
Got questions? We have answers.